I was happily building some code to filter and manage traffic in Open vSwitch via C++ communicating via the OpenFlow interface. Then, ... well, I realized I was missing some things. In OVS's documentation, much of it uses the command line tools to inject the rules. Some of those examples show automatic mac swaps and such. hmm, Nicera extensions but not in the openflow specification. Which means changing code to interface to other api bind points of OVS.
I had also written some code to interface to the OVSDB so I could list interfaces, detect changes, and obtain statistics.
In stepping back and thinking about this, I came across a youtube video on youtube:
which talks about Stratum and Next-Gen SDN. I wasn't so interested in the Stratum concept in as much as I was interested in the p4.org concept of writing code to filter packets.
From a Linux network stack perspective, a little closer to home, there is eBGP and XDP. The best diagram I've seen of XDP and eBGP hook points is on page 3 of 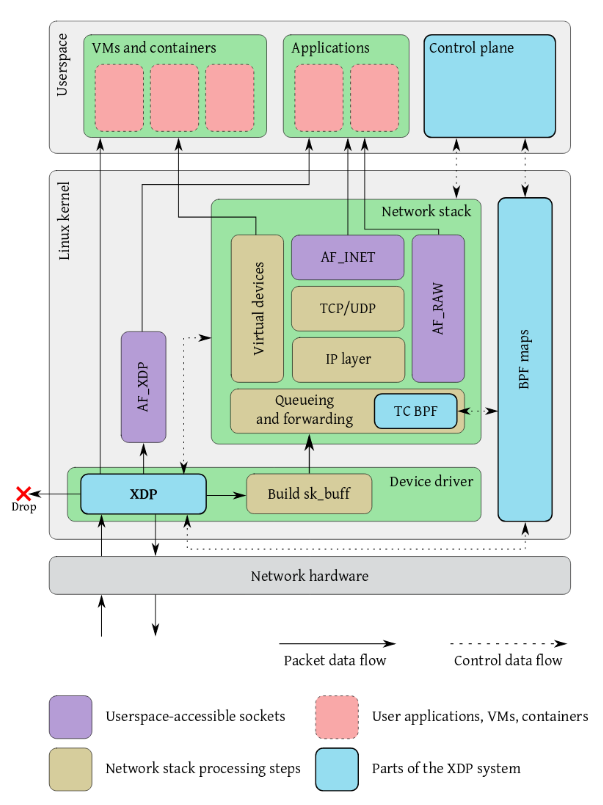 The eXpress Data Path: Fast Programmable Packet Processing inthe Operating System Kernel which was presented at
2018 SigComm CoNEXT Conference. As an aside, another interesting paper there is "
Leveraging eBPF for programmable network functions with IPv6 Segment Routing".
The eXpress Data Path: Fast Programmable Packet Processing inthe Operating System Kernel which was presented at
2018 SigComm CoNEXT Conference. As an aside, another interesting paper there is "
Leveraging eBPF for programmable network functions with IPv6 Segment Routing".
Other references:
- BPF and XDP Reference Guide
- BPF Compiler Collection (BCC)
- Linux Plumbers Conference 2018 BPF Microconference
- Linux Plumbers Conference 2018 Networking Track
- Linux Bridge, l2-overlays, E-VPN!
- Scaling bridge forwarding database
- Lifetime of BPF objects
- P4-16 Language Specification
- net: add bpfilter
- AF_XDP
- Linux Network Programming with P4
- bpf - perform a command on an extended BPF map or program
- BPF - BPF programmable classifier and actions for ingress/egress queueing disciplines
- 7 tools for analyzing performance in Linux with bcc/BPF - gethostlatency, tcplife, biolatency, opensnoop, execsnoop, ...
In Debian with Kernel "4.19.0-1-amd64 #1 SMP Debian 4.19.12-1 (2018-12-22)", the following are set:
# grep -i bpf /boot/config-4.19.0-1-amd64 CONFIG_CGROUP_BPF=y CONFIG_BPF=y CONFIG_BPF_SYSCALL=y # CONFIG_BPF_JIT_ALWAYS_ON is not set CONFIG_IPV6_SEG6_BPF=y CONFIG_NETFILTER_XT_MATCH_BPF=m # CONFIG_BPFILTER is not set CONFIG_NET_CLS_BPF=m CONFIG_NET_ACT_BPF=m CONFIG_BPF_JIT=y # CONFIG_BPF_STREAM_PARSER is not set CONFIG_LWTUNNEL_BPF=y CONFIG_HAVE_EBPF_JIT=y CONFIG_BPF_EVENTS=y # CONFIG_BPF_KPROBE_OVERRIDE is not set CONFIG_TEST_BPF=m # grep -i xdp /boot/config-4.19.0-1-amd64 # CONFIG_XDP_SOCKETS is not set
Install the the BPF Compiler Tools with:
apt install libbpfcc libbpfcc-dev bpfcc-tools python-bpfcc
bcc header files are in '/usr/include/bcc/'. Many tools with suffic 'bpfcc' are installed in /usr/sbin. There is a man page for each. Many many examples can be found in /usr/share/doc/bpfcc-tools/examples/doc/.
7 tools for analyzing performance in Linux with bcc/BPF covers execsnoop, opensnoop, xfsslower, biolatency, tcplife, gethostlatency and trace. The article also refers to bcc Python Developer Tutorial. Also referenced was bpftrace. A better page referencing these tools is Linux Extended BPF (eBPF) Tracing Tools. eBPF: One Small Step is an early Brendan Gregg article on eBPF tracing.
Going even deeper into the woods, another tool referenced includes SystemTap which has a Debian Package.
The BCC has a reference guide. Most of the preceding has to do with tracing. Now to get to packet manipulation.
For compiling, some packages:
apt install clang llvm clang-7-doc ncurses-doc libomp-7-doc llvm-7-doc
Some items from Making the Kernel’s Networking Data Path Programmable with BPF and XDP:
- 11 64bit registers, 32bit subregisters, up to 512bytes stack
- Instructions 64bit wide, max 4096 per program
- BPF calling convention for helpers allows for efficient mapping: a) R0 →return value from helper call, b) R1 - R5 →argument registers for helper call, c) R6 - R9 → callee saved, preserved on helper call
- /proc/kallsyms exposure of JIT image as symbol for stack traces
- Since LLVM 3.7: clang -O2 -target bpf -c foo.c -o foo.o
- To show ability: llc --version | grep bpf
- Assembler output through -S supported
- llvm-objdump for disassembler and code annotations (via DWARF)
- C example walkthrough: tools/testing/selftests/bpf/testl_4lb.c
- when attaching to generic XDP kernel driver via iproute2: ip link set dev eno1 xdpgeneric obj prog.o
2019/05/04 - Hacker News had a reference to CloudFlare where they discussed eBPF can't count?! - an article with references on how to debug eBPF code.


